Aluminium House Wire Wound Resistors
The ARCOL power resistor name has been an established name in resistors for the European market for 70 years. They are most famous for their aluminum housed wirewound resistors. The aluminum housed resistors gained popularity for their robust design and high wattage capabilities. Arcol has since expanded its product offering to other technologies and mounting styles.

ARCOL HS Series
Manufactured in line with the requirements of MIL 18546 and IEC 115, designed for direct heatsink mounting with thermal compound to achieve maximum performance.
Read More View in Catalog
ARCOL HS Series 400-600
The ARCOL HS400-600 aluminum housed resistors are designed to be mounted to a heatsink to achieve maximum wattage. These resistors are suitable for power applications including braking resistors for frequency converters.
Read More View in Catalog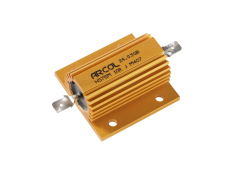
ARCOL HS (M) Series
Manufactured in line with the requirements of MIL 18546 and IEC 115, designed for direct heatsink mounting with thermal compound to achieve maximum performance.
Read More View in Catalog
ARCOL HSW Series
Manufactured in line with the requirements of MIL 18546 and IEC 115, designed for direct heatsink mounting with thermal compound to achieve maximum performance.
Read More View in Catalog
ARCOL ACD22 Counting Dial
22mm, 10 turns counting dial in satin-chrome finish, for precision potentiometers and other rotating devices.
Read More View in Catalog
ACD46
46mm, 15 turns counting dial in satin-chrome finish, for precision potentiometers and other rotating devices.
Read More
Arcol ACS Series
The ACS resistor provides a good balance of power density, stability, and resistance to environment for a broad range of industrial applications, such as drives and controls.
Read More
ARCOL AP725 Series
The ARCOL AP725 provides power dissipation up to 20 watts with a proper heatsink.
Read More View in Catalog
ARCOL AP830 Series
A high power TO-220 style resistor package designed for high frequency emitter circuits in switching power supplies.
Read More View in Catalog
ARCOL AP836 Series
A high power TO-220 style resistor package designed for high frequency emitter circuits in switching power supplies.
Read More View in Catalog
ARCOL AP851 Series
A high power TO-220 style resistor package designed for high frequency emitter circuits in switching power supplies.
Read More View in Catalog
Arcol APC Series
The Arcol APC Precision Chip Resistor uses thin film tehcnology with a wide resistance range, very tight tolerance, and a very low TCR.
Read More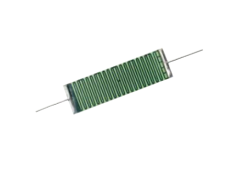
ARCOL ARC1 Series
Resistors for voltage dividers, medical measuring equipment, electrostatic & current-limiting devices where high stability, low TCR, & high ohmic values are required.
Read More View in Catalog
ARCOL ARC2 Series
Resistors for voltage dividers, medical measuring equipment, electrostatic & current-limiting devices where high stability, low TCR, & high ohmic values are required.
Read More View in Catalog
ARCOL ARC3 Series
We offer resistors for voltage dividers, medical measuring equipment, electrostatic, and current limiting devices where high stability, low TCR, & high ohmic values are required.
Read More View in Catalog
ARCOL ARF Series
ARF Low Profile Wirewound Metal Clad Resistors offer a flexible design with high pulse capability. They are ideally suited to braking and inverter/converter applications
Read More View in Catalog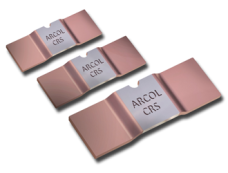
ARCOL CRS Series
Available in two sizes ARCOL’s CRS utilizes Electron Beam Welding technology to connect its Manganin or NiCr element to heavy copper connectors.
Read More View in Catalog
Arcol FPA100 Series
The Arcol FPA100 series are non-inductive thick film resistors ideally suited for high frequency and pulse load applications
Read More
ARCOL FPA250 Series
250 Watt resistor designed for various applications including power transmission, traction, variable speed drives, power supplies, robotics, motor control and power control devices.
Read More View in Catalog
ARCOL FPA350 Series
350 Watt resistor designed for various applications including power transmission, traction, variable speed drives, power supplies, robotics, motor control and power control devices.
Read More View in Catalog
ARCOL FPA600 Series
600 Watt resistor designed for various applications including power transmission, traction, variable speed drives, power supplies, robotics, motor control and power control devices.
Read More View in Catalog
ARCOL FPA800 Series
For variable speed drivers, power supplies, control devices, robotics, motor control and other power designs. The easy mounting fixture guarantees an auto calibrated pressure to the cooling plate of 120 to 160N
Read More View in Catalog
ARCOL FPA2K Series
For variable speed drivers, power supplies, control devices, robotics, motor control and other power designs. The easy mounting fixture guarantees an auto calibrated pressure to the cooling plate of approx. 300 N.
Read More View in Catalog
Arcol KABR Series
The Arcol KABR series are wirewound metal clad braking resistors with excellent stability, reliability, and mechanically rigid.
Read More
ARCOL L4T Series
The L4T Series, brought to you by ARCOL, boasts a TCR of 75PPM with 50PPM available.
Read More View in Catalog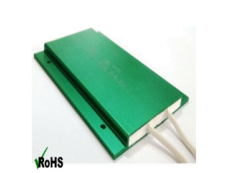
Arcol LPR Series
LPR series are low profile resistors encapsulated in an ultra slim aluminium housed casing. Designed for applications where space is critical i.e EV vehicles,instruments, drivers and frequency converters.
Read More
ARCOL MRA Series
Europe’s No 1 selling axial thin film high precision resistor.
Read More View in Catalog
Arcol MSR Series
LPR series are low profile resistors encapsulated in an ultra slim aluminium housed casing. Designed for applications where space is critical i.e EV vehicles,instruments, drivers and frequency converters.
Read More
ARCOL RWS Series
A compact and precision power resistor, manufactured to the highest standards.
Read More View in Catalog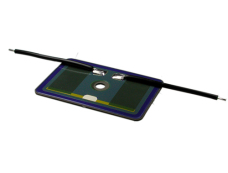
ARCOL TFBR Series
The TFBR series provides high power density in a low profile package.
Read More View in CatalogWhy Should You Partner with Ohmite?
Stability: Leader in Resistive Technology for 100 Years
Ohmite has manufactured resistors for 100 years! We've demonstrated a proven track record of creating quality resistive products for high power, high energy, and high voltage applications.
Flexibility: We are Experienced Problem Solvers
Whether it's our expansive catalog of standard parts, our many customization options for each series, or our ability to develop brand new products based on customer designs, Ohmite is dedicated to solving engineers' problems.
Accessibility: We're Here to Help as Trustworthy Partner
Ohmite's team of engineers are available to explain our technology, answer your questions, and consult on important design decisions to help make our customers' lives easier.